Leading Functions of the Best Cyber Security Services in Dubai You Need To Know
Leading Functions of the Best Cyber Security Services in Dubai You Need To Know
Blog Article
Understanding the Various Kinds of Cyber Security Services Available Today
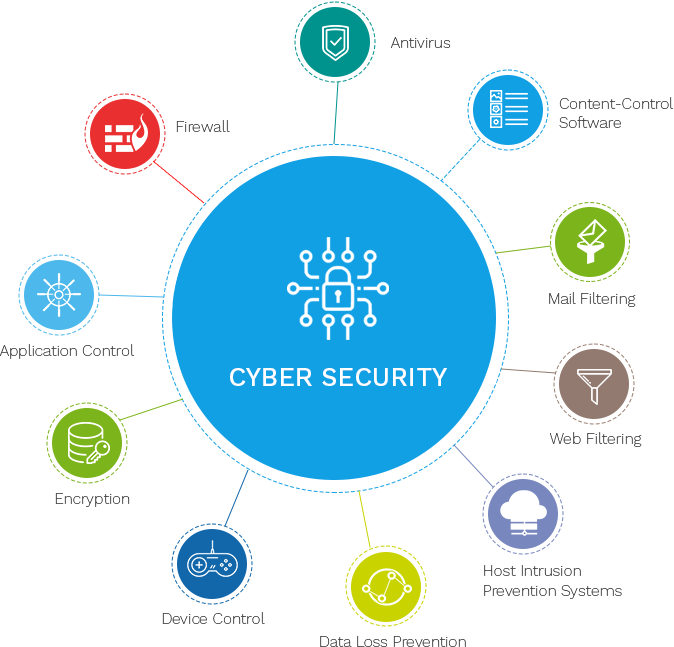
In today's electronic landscape, comprehending the varied array of cyber protection services is essential for securing business data and facilities. With risks coming to be significantly sophisticated, the function of anti-viruses and anti-malware options, firewalls, and invasion detection systems has actually never ever been a lot more crucial. Managed protection solutions provide constant oversight, while data security continues to be a foundation of details protection. Each of these services plays an unique role in a detailed security technique, however exactly how do they connect to create an impervious defense? Exploring these complexities can disclose much concerning crafting a resistant cyber protection stance.
Anti-virus and Anti-Malware
In today's electronic landscape, antivirus and anti-malware services are vital elements of extensive cyber protection techniques. These tools are made to identify, prevent, and reduce the effects of risks positioned by harmful software application, which can compromise system integrity and access delicate information. With cyber threats advancing rapidly, deploying anti-malware programs and robust antivirus is vital for safeguarding electronic assets.
Modern anti-viruses and anti-malware solutions utilize a mix of signature-based detection, heuristic evaluation, and behavioral tracking to recognize and reduce dangers (Best Cyber Security Services in Dubai). Signature-based discovery depends on data sources of known malware signatures, while heuristic evaluation examines code behavior to recognize possible dangers. Behavioral monitoring observes the activities of software program in real-time, making sure prompt identification of questionable tasks
Real-time scanning guarantees constant security by checking files and processes as they are accessed. Automatic updates keep the software current with the newest danger knowledge, reducing vulnerabilities.
Incorporating reliable anti-viruses and anti-malware remedies as part of a total cyber security structure is indispensable for protecting versus the ever-increasing array of electronic hazards.
Firewall Programs and Network Safety
Firewall softwares act as an essential part in network security, serving as an obstacle between relied on interior networks and untrusted external settings. They are developed to monitor and regulate inbound and outgoing network web traffic based on predetermined safety rules. By developing a protective border, firewall softwares help protect against unauthorized accessibility, making certain that only reputable website traffic is allowed to go through. This safety procedure is essential for safeguarding sensitive information and maintaining the honesty of network framework.
There are different sorts of firewall programs, each offering distinctive capacities tailored to particular safety and security needs. Packet-filtering firewall softwares evaluate data packets and permit or block them based upon source and destination IP ports, methods, or addresses. Stateful examination firewall programs, on the other hand, track the state of active connections and make dynamic choices based on the context of the traffic. For advanced protection, next-generation firewall softwares (NGFWs) integrate additional features such as application understanding, invasion prevention, and deep packet evaluation.
Network security expands beyond firewalls, encompassing a range of practices and modern technologies created to secure the use, reliability, stability, and security of network facilities. Applying robust network safety and security actions ensures that companies can safeguard against progressing cyber dangers and preserve protected interactions.
Intrusion Discovery Solution
While firewalls develop a defensive perimeter to manage website traffic flow, Breach Detection Equipment (IDS) offer an additional layer of protection by checking network activity for questionable behavior. Unlike firewalls, try here which largely focus on filtering system incoming and outbound web traffic based upon predefined regulations, IDS are designed to identify prospective threats within the network itself. They function by examining network traffic patterns and determining abnormalities indicative of harmful tasks, such as unauthorized gain access to attempts, malware, or policy violations.
IDS can be classified right into 2 primary kinds: network-based (NIDS) and host-based (HIDS) NIDS are released at calculated points within the network facilities to monitor website traffic throughout multiple tools, offering a wide sight of prospective threats. HIDS, on the other hand, are set up on specific tools to assess system-level activities, supplying an extra granular viewpoint on safety occasions.
The effectiveness of my link IDS relies heavily on their trademark and anomaly detection abilities. Signature-based IDS contrast observed events against a data source of recognized danger trademarks, while anomaly-based systems determine inconsistencies from developed typical habits. By implementing IDS, organizations can enhance their ability to identify and respond to dangers, hence enhancing their general cybersecurity pose.
Managed Protection Provider
Managed Security Services (MSS) stand for a critical method to strengthening a company's cybersecurity structure by contracting out specific protection features to specialized suppliers. This design allows services to utilize specialist resources and progressed modern technologies without the requirement for considerable in-house financial investments. MSS carriers use a detailed variety of services, consisting of surveillance and handling intrusion discovery systems, susceptability analyses, hazard knowledge, and event response. By entrusting these essential tasks to professionals, companies can make sure a robust protection versus evolving cyber hazards.

Cost efficiency is another significant advantage, as companies can avoid the considerable expenses connected with structure and maintaining an internal safety click site team. Furthermore, MSS offers scalability, allowing companies to adapt their safety steps in accordance with growth or altering hazard landscapes. Inevitably, Managed Security Providers provide a calculated, reliable, and reliable ways of guarding a company's digital assets.
Information File Encryption Techniques
Information file encryption methods are essential in protecting sensitive info and guaranteeing data integrity throughout electronic platforms. These techniques convert information into a code to stop unapproved accessibility, consequently protecting confidential details from cyber dangers. Encryption is important for protecting information both at rest and in transportation, providing a robust protection mechanism versus data breaches and making sure conformity with information security policies.

In addition, emerging strategies like homomorphic file encryption permit computations on encrypted information without decryption, preserving personal privacy in cloud computer. Essentially, data security techniques are essential in modern-day cybersecurity strategies, protecting information from unauthorized accessibility and maintaining its privacy and integrity.
Final Thought
The varied array of cybersecurity services offers a comprehensive defense approach vital for safeguarding digital assets. Antivirus and anti-malware options, firewall softwares, and invasion discovery systems collectively boost risk detection and avoidance capacities. Managed security solutions offer constant surveillance and specialist incident response, while information encryption techniques guarantee the privacy of delicate information. These services, when integrated successfully, develop an awesome obstacle against the dynamic landscape of cyber dangers, strengthening a company's strength despite potential cyberattacks - Best Cyber Security Services in Dubai.
In today's electronic landscape, recognizing the diverse range of cyber safety and security solutions is essential for safeguarding business data and framework. Managed security solutions offer continual oversight, while information file encryption stays a cornerstone of details security.Managed Security Provider (MSS) stand for a strategic strategy to boosting an organization's cybersecurity framework by outsourcing specific safety features to specialized companies. Furthermore, MSS provides scalability, enabling organizations to adapt their safety steps in line with growth or changing threat landscapes. Managed safety solutions offer constant monitoring and professional event response, while information file encryption strategies guarantee the discretion of delicate details.
Report this page